Optimize online payment security with our WAF

Payment methods represent the most critical attack surface in omnichannel retail. Within a SaaS architecture, a WAF plays a key role in securing transactional flows, ensuring the availability of checkout journeys, and meeting compliance requirements. When properly integrated, it protects payments without compromising the customer experience.
Payment security: the pillar of trust in modern retail
For major retail brands, the completion of a purchase is the ultimate moment of truth. Whether a customer uses their smartphone in the aisles, orders from home, or uses a self-checkout terminal, any security concern can instantly shatter years of loyalty. While an HTTPS padlock is a basic requirement, it is merely the tip of the iceberg in the digital fortress that IT and marketing teams must build to safeguard their point of sale (POS) network and e-commerce platform.
Within an omnichannel or unified commerce environment, the challenge is multifaceted. It is no longer enough to simply secure a website; you must protect an entire ecosystem where customer data flows seamlessly between the ERP, the digital storefront, and in-store payment terminals.
Securing online payments effectively
Imagine your potential customer poised to complete an online purchase. The product is in their cart, they are ready to reach for their credit card… and suddenly, a moment of hesitation. They instinctively look for the small padlock in the address bar. It’s there, but is it truly enough to guarantee the safety of their payment details? The reality of security goes far deeper than that simple green icon.
This padlock, which indicates an HTTPS connection, is absolutely vital. It ensures that card data is encrypted and unreadable as it travels from the user’s device to the website. However, security experts agree that this does nothing to protect the “house” at the end of the journey. If the website itself has a back door or vulnerability, the data remains exposed the moment it arrives at its destination.
This is where an invisible guardian comes into play a crucial layer of protection that most people never notice during online transactions. Behind the scenes of reputable websites, a digital shield analyzes every visitor before they even interact with the page. This guardian is known as a Web Application Firewall (WAF). Understanding its role is the real key to securing online payments and allowing customers to shop with total confidence.
The HTTPS padlock: what it really protects (and what it doesn’t)
The padlock symbol next to a website address signifies the HTTPS protocol, which is a vital first step. It proves that the connection between your browser and the website is private and encrypted.
Think of the HTTPS protocol as a sealed envelope. When you enter your card details, it places them inside this envelope before sending them across the internet, ensuring no one can peek inside during transit. This step is critical for data-in-motion security, preventing your personal information from being intercepted by prying eyes along the way.
However and this is a fundamental distinction the padlock says nothing about the reliability of the recipient holding the envelope. A fraudulent site can easily obtain a valid certificate to appear legitimate. While HTTPS confirms that data reaches the intended site, it does not guarantee that the site is trustworthy or that its internal security is airtight. In reality, the protection of customer data (GDPR) only truly begins once the site has received your information.
Major risks for retail chains
The padlock is essential, but it is only one piece of the puzzle. The real question is: once the data arrives, how well is it guarded? To truly secure a payment gateway and maintain customer trust, the website itself must be shielded against forced entry.
HTTPS ensures that your customers’ data is encrypted while in transit. However, for a major retail chain, the primary risk isn’t message interception it’s the vulnerability of the destination itself. If your commerce platform has a flaw, that information becomes exposed the moment it is received.
This is where the Web Application Firewall (WAF) becomes indispensable. For a retailer processing millions of transactions, the WAF acts as an elite security detail stationed at every digital touchpoint. It analyzes visitor behavior in real-time, neutralizing intrusion attempts before they can ever reach your customer databases.
The real threat: large-scale data skimming
For hackers, the ultimate “prize” isn’t a single transaction; it is compromising a brand’s central database containing names, purchase histories, and loyalty profiles. A breach through a simple contact form or search bar can trigger a massive data leak, devastating your brand image and violating GDPR compliance.
The true threat: when the website itself becomes the entry point
Your sealed envelope (the HTTPS connection) has reached its destination safely. But what if the house receiving it has open windows and unlocked doors? This is the exact problem with an unsecured website. Hackers often bypass the encrypted tunnel which is too difficult to crack and focus their efforts directly on the site, searching for the smallest vulnerability to exploit.
These vulnerabilities are rarely reinforced doors that need to be kicked down; they are usually the everyday entry points you rely on. A contact form, a search bar, or even a review section can be hijacked. Instead of a standard message, an attacker might insert malicious code. These hidden commands act like a digital crowbar, tricking the system into opening a back door.
Their objective is rarely limited to a single credit card. The true treasure is the entire database: a comprehensive list of customers, including names, email addresses, purchase histories, and occasionally payment details. This type of attack a form of online data skimming can compromise thousands of customers simultaneously, making credit card fraud prevention significantly more complex.
Security, therefore, does not end with the padlock. Every area where a visitor can interact is a potential gateway that needs protection. But how can a site owner monitor all these entry points simultaneously and distinguish a legitimate shopper from a disguised intruder? This is where an essential first line of defense is required.
What is a WAF? The invisible guardian protecting your favorite sites
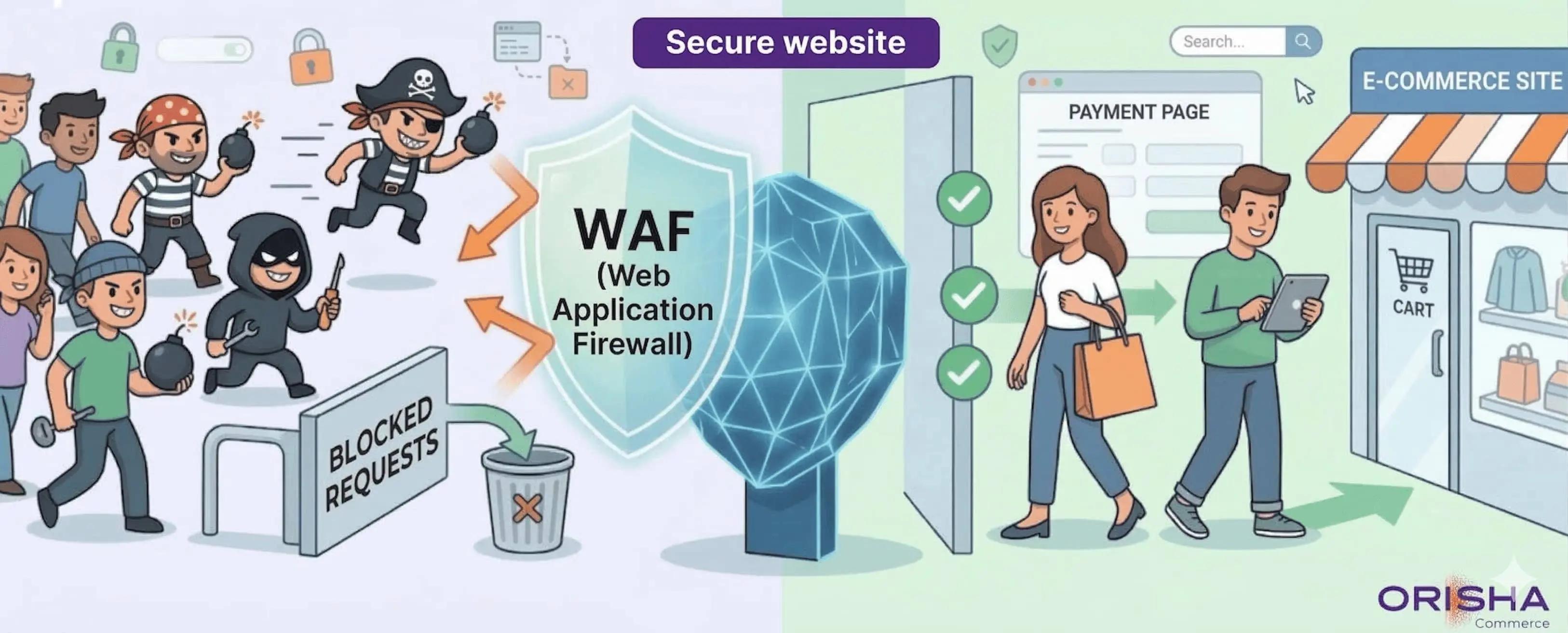
Given the numerous entry points a hacker might exploit, how can a website defend itself? You cannot simply shut down your contact forms or search bars. The solution is to station a vigilant guard at the entrance. This guard is the Web Application Firewall (WAF) a security shield positioned between the internet and your website that scrutinizes everything attempting to gain access.
To easily understand what a WAF does for e-commerce, imagine a bouncer at an exclusive nightclub. Their job isn’t just to count heads; they scrutinize every individual, checking their behavior and intent before allowing them in. If someone appears suspicious or tries to smuggle in a prohibited item, they are turned away at the door immediately, no questions asked.
In the digital realm, this guardian inspects every request sent to the site whether it’s a click, a login attempt, or a form submission. It is trained to recognize the most common attack signatures, such as hidden malicious code. As soon as a suspect request is detected, the WAF blocks it instantly, stopping the hacker in their tracks before they can even reach the site or its sensitive data.
This proactive approach is the core strength of a WAF. Unlike an antivirus, which often reacts after a system has been infected, the WAF prevents the threat from entering in the first place. It doesn’t just clean up the damage; it ensures the damage never occurs. But how exactly does this digital guardian tell the difference between a legitimate shopper and a disguised attacker on a checkout page?
How a WAF actually blocks attacks on a payment page
This digital guardian doesn’t rely on guesswork. To distinguish an honest customer from a hacker, the WAF employs a highly effective method: “attack signature” recognition. Imagine it holds a massive, constantly updated catalog describing thousands of known hacking techniques. Every request hitting the site is cross-referenced with this catalog in a split second as if the bouncer had memorized the face of every troublemaker on earth.
In practice, a hacker on a checkout page might attempt to enter malicious code into the “Address” field instead of a real location. Their goal is to trick the site’s database into revealing confidential data, such as other customers’ details. To you, this attempt is invisible. However, the WAF detects it instantly, identifies the code as a known attack signature, and shuts down the request immediately. The hacker hits a wall, and both the site and your information remain perfectly safe.
Through this constant vigilance, the WAF neutralizes a broad spectrum of threats before they can reach the core of the site. Specifically, it prevents:
- Attempts to steal customer lists.
- Malicious code injection within contact or payment forms.
- Various forms of identity theft aimed at gaining unauthorized account access.
The WAF serves as an indispensable shield for the website itself. Yet, one question remains: if the WAF protects the site, what protects your actual credit card numbers during the transaction? This is where another essential security player steps in.
Beyond the WAF: why sites (almost) never store card numbers
Even with a WAF on guard, would you hand over your vault keys to just anyone? Likely not. This is why reputable e-commerce sites follow a fundamental principle: they almost never handle your credit card information directly. At the point of payment, the site hands over the process to an ultra-secure specialist a payment gateway like Stripe, PayPal, or a banking solution. Think of it as the digital equivalent of an in-store electronic payment terminal.
These gateways utilize a technology known as payment information tokenization. The concept is both simple and powerful: instead of transmitting your actual card number, the gateway replaces it with a unique, encrypted identifier a “token.” This token acts as a one-time code valid only for that specific transaction on that specific site. Should a thief intercept it, it would be entirely worthless to them.
Under this system, the merchant site never stores your full card number. All they retain is a token with no intrinsic value much like a digital transaction receipt. For a hacker, breaching such a database would be a massive disappointment; they would find no card numbers to steal, only unusable codes. This practice adheres to strict security standards (PCI DSS) and drastically reduces overall risk.
You can now see the powerful duo safeguarding your transactions. The WAF protects the “container” the website itself from forced entry, while tokenization protects the “content” your payment data by making it worthless if stolen. Together, these two layers of defense ensure that online shopping is as secure as, if not more so than, buying in-store.
WAF and payment platforms: double-lock security
Once the WAF confirms your request is safe, the transaction is handed to a payment gateway think of it as a digital armored truck. The shop doesn’t transport the money to the bank themselves; they rely on a specialized, ultra-secure company to do it. These payment solutions are engineered with a single goal: to handle your funds within a hermetically sealed environment.
This setup creates multi-layered security a genuine double-lock. The WAF acts as the guard watching over the entire store, while the payment gateway serves as the mobile vault securing the money itself. Furthermore, the gateway often replaces your actual card number with a one-time token, reinforcing online transaction security. Consequently, the e-commerce site never needs to store your full banking details, significantly lowering the risk of exposure.
The distinction is crucial: the WAF protects the application (the website), while the gateway protects the financial transaction. Together, they provide defense-in-depth, governed by precise regulatory standards.
PCI DSS, PSD2: the “rules of the road” for online security
These regulations function much like building codes for a physical structure. Standards with complex names like PCI DSS (for card data) or PSD2 (for European payments) serve as mandatory building codes for any site that manages your money.
At the heart of these requirements, one element is often non-negotiable: to ensure PCI DSS compliance, a Web Application Firewall is required. These standards compel companies to implement and maintain a WAF for PSD2 compliance. They mandate specific WAF rules for transaction security, ensuring your “digital guard” is always capable of identifying the latest threats.
In practice, this means your security isn’t left to the whims of a merchant site. It is governed by strict specifications, often verified by independent auditors. This provides the assurance that robust protection is in place before you even add an item to your cart.

The Orisha Commerce approach: native security for unified commerce
To meet these challenges, Orisha Commerce provides solutions such as Openbravo POS, engineered to embed security at the heart of the shopping journey.
- Compliance and advanced protocols: Our solutions adhere to the most stringent standards, including PCI DSS compliance, ensuring that every transaction whether online or via mobile POS is handled with rigorous security protocols.
- Strategic partnership with Sipay: Through our collaboration with industry experts like Sipay, Orisha Commerce delivers a robust payment gateway capable of navigating the complexities of unified omnichannel retail.
- Tokenization: Rendering data useless to fraudsters: Rather than storing credit card numbers, our systems utilize tokenization. The card number is replaced by a unique, encrypted “token.” Should a retailer’s server be compromised, a hacker would find only worthless codes, rendering the theft completely fruitless.
Beyond technology: turning security into a marketing asset
For major brands, security should not be viewed as a hurdle, but as a conversion driver. A seamless experience, where the customer feels protected at every touchpoint, is the absolute foundation of loyalty.
Checklist for major brand management:
- Centralization: Are you using a single platform like Openbravo Commerce Cloud to centralize transaction traceability?
- Touchpoint Audit: Are your mobile POS solutions and kiosks protected by the same security standards as your e-commerce?
- Transparency: Do you communicate clearly with your customers regarding data protection (GDPR) and payment security?
Conclusion: navigating with confidence in the age of AI and GEO
As AI tools (like Google AI Overviews) begin to recommend solutions based on brand reputation and reliability, your payment security becomes an indirect visibility factor (GEO – Generative Engine Optimization). By partnering with Orisha Commerce, you safeguard your assets while ensuring the lasting authority of your brand in the marketplace.
Would you like a demonstration of our secure checkout solutions for your store network?
FAQ
Why are payment methods a primary target in retail?
Payment journeys centralize highly sensitive data and critical transactional flows. In omnichannel retail, these flows are constantly exposed through e-commerce, POS systems, and APIs, making them prime targets for automated attacks and fraud.
What role does a WAF play in securing retail payments?
A WAF safeguards payment applications and APIs from application-layer attacks (such as bots, injections, and request abuse) by filtering out malicious traffic in real-time, all without disrupting legitimate transactions.
Is a WAF enough to secure SaaS payments?
No. While a WAF is an essential component, it is part of a broader, holistic security strategy that includes encryption, identity management, flow monitoring, and regulatory compliance.
Can a WAF impact payment performance?
When properly configured within a Cloud SaaS architecture, a WAF does not introduce any noticeable latency. In fact, it helps maintain the availability of payment services during heavy traffic spikes.
How does a WAF contribute to retail payment compliance?
By shielding exposed applications and ensuring detailed access traceability, a WAF is instrumental in securing transactional data and meeting the regulatory requirements governing payments.